Check Point Management-HA and SecureTrack (2)
Nearly since the first versions of Tufin SecureTrack, Check Point Management-HA has been supported by Tufin. The requirements at that time were not as high as today and the software has been much more simple than today.
In an earlier article about Check Point Management-HA some restrictions of SecureTrack have been pointed out (regarding e.g. Ticket-IDs or certification dates for rules). Today, there are further "specialities" when using the Rule Viewer.
Actual versions don't consider the mechanism of Check Point Management-HA (not even in the data base). So if two Management Servers are connected to SecureTrack, each rule is shown twice (also if the secondary Management is imported correctly to SecureTrack using https://<ST>/tools).
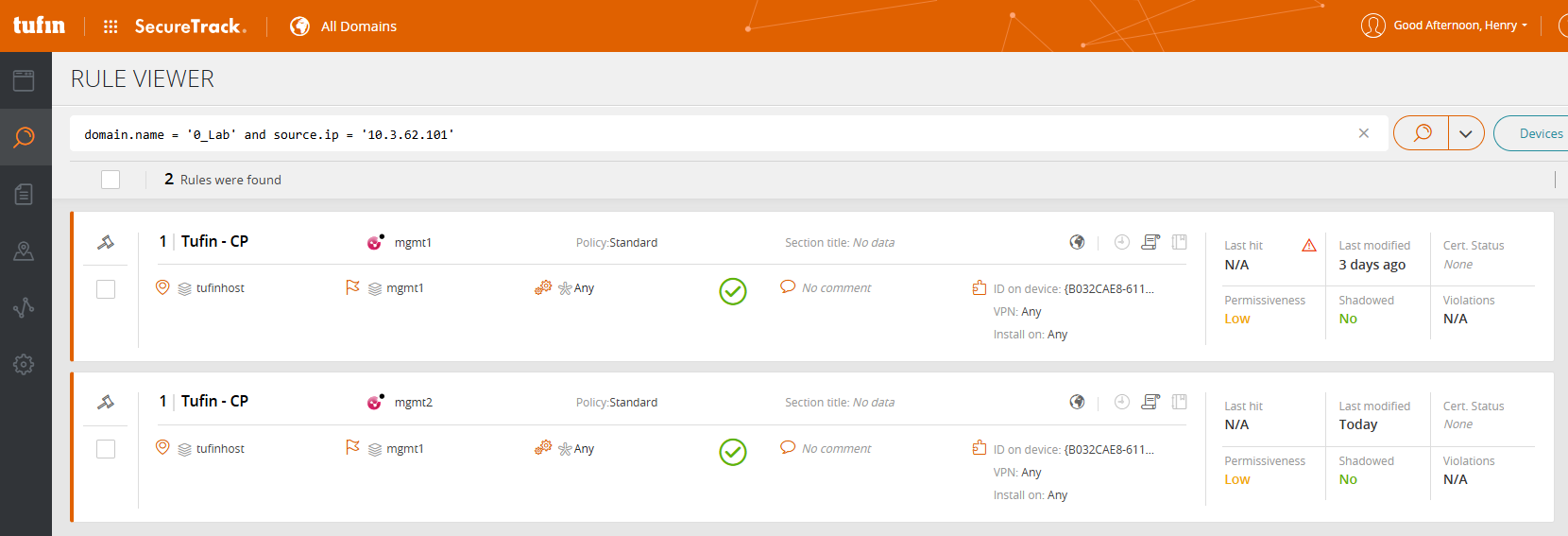
Following Tufin Support, the official workaround is to filter also for the Device ID of one of the two Check Point Management Servers. And, it's recommended to open a Request for Enhancement (RFE) asking Tufin to improve the functionality when Check Point Management-HA is deployed.